Profile Applicability: Level 1
Description:
SSH (Secure Shell), which is used for remote access in CLI mode to the system, to connect with instances, mainly Linux, we must set up the rule to authorize SSH traffic from the base computer’s public IPv4 address.
Security groups provide stateful filtering of ingress/egress network traffic to AWS resources. These groups should not permit unrestricted access from the internet to SSH (port 22).
Rationale:
Removing unfettered connectivity to remote console services, such as SSH, reduces a server's exposure to risk.
Impact:
If we permit all IP addresses to access the instance using SSH, it is unsafe for production environments. So that for any organization or in production, it is good practice to authorize only a specific IP address or range of addresses to access the instance to reduce the rate of risk of an attack.
Note:
For updating an existing environment, care should be taken to ensure that administrators currently relying on an existing ingress from 0.0.0.0/0 have access to ports 22 and/or 3389 through another security group.
Default Value:
The following table describes the default rules for a default security group:-
Inbound |
|
|
|
|
|---|---|---|---|---|
Type | Protocol | Port Range | Source | Description |
All traffic | All | All | Security Group ID | For the associated instances, inbound traffic allows network interfaces to be assigned to the same security group. |
Pre-Requisite
Before we start this first Decide who access the instance a single host or a specific network who is authorized person’s base machine.
To connect your instance you must set up a rule to authorize SSH traffic
We need to find out the range of IP addresses used by client computers.
Remediation:
Test Plan:
Perform the following to determine if the account is configured as prescribed:
Log in to the AWS Management Console
Go to EC2 service
Click on the Security Groups in the left navigation pane
Select the security group you want to examine
Click the Inbound Rules tab
Ensure no rule exists that has a port range that includes port 22 and has a Source of 0.0.0.0/0
Using CLI Commands:
aws ec2 describe-security-groups --filters Name=ip-permission.cidr,Values='0.0.0.0/0' \
--query "SecurityGroups[*].{Name:GroupName,ID:GroupId}"Remediation:
Implementation Steps:
Perform the following to implement the prescribed state:
- Log in to the AWS Management Console at https://console.aws.amazon.com/vpc/home
- Go to EC2 service
- In the left pane, click Security Groups

- For each security group, perform the following
- Select the security group

- Click the Inbound Rules tab

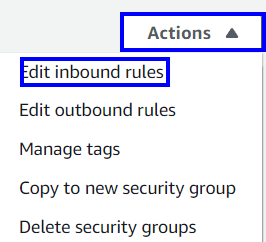
- Click Edit inbound rules button to change the Inbound rules to the specific IP addresses.

- change the inbound traffic rule as SSH port range 22.

- Click on the Save rules button to save the changes made.

Note:
Using AWS CLI:
To remove the rule:
aws ec2 revoke-security-group-ingress \
--group-id <value> --protocol <protocol> \
--port 22 --cidr 0.0.0.0/0
Backout Plan:
1. Sign into the AWS Management Console.
2. Go to EC2 dashboard at https://console.aws.amazon.com/ec2/.
3. Click on Security Groups, under the NETWORK & SECURITY section, in the left navigation pane
4. Open the security group by clicking on the security group ID
5. Click on Actions dropdown and select Edit inbound rules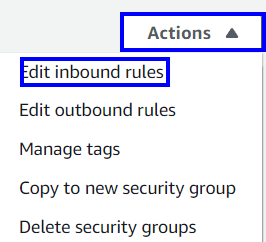
6. Click on Edit inbound rules button and select Type “All traffic” Protocol “All “ and port range “All” and save it.
Using AWS CLI:
aws ec2 authorize-security-group-ingress
--group-id <value>
--protocol all
--port all
Reference
CIS Controls:
9.2 Ensure Only Approved Ports, Protocols, and Services Are Running
- Ensure that only network ports, protocols, and services listening on a system with validated business needs, are running on each system.
aws ec2 revoke-security-group-ingress \
--group-id <value> --protocol <protocol> \
--port 22 --cidr 0.0.0.0/0
aws ec2 authorize-security-group-ingress
--group-id <value>
--protocol all
--port all




