Profile Applicability: Level 2
Description:
VPC flow logs as a feature that permits you to record information about the IP traffic going to and from the network interface in your VPC. After you've created a flow log, you can view and retrieve its data in Amazon CloudWatch Logs.
Rationale:
VPC Flow Logs provide visibility into network traffic that traverses the VPC and can be used to detect anomalous traffic or insight during security workflows.
Impact:
Once enabled, the Flow Logs feature will start collecting network traffic data to and from your Virtual Private Cloud (VPC), data that can be useful to detect and troubleshoot security issues and make sure that the network access rules are not overly permissive.
Default Value:
VPC flow is not enabled by default, Enabling VPC flow logs for all VPC Will increase the security and reduce compliance issues.
Pre-Requisite:
There must be at least one VPC enabled in the AWS account
Ensure Cloudwatch or S3 bucket is created for VPC flow log for retrieving the VPC flow log Data
After auditing, if you notice logging is not enabled then only go to remediation steps
Remediation:
Test plan:
1. Sign in to the AWS Management console
2. Navigate to VPC service at https://console.aws.amazon.com/vpc/
3. In the left navigation pane, select Your VPCs, You will see a list Of VPCs that already exists
4. Click on the VPC that you want to examine and select the Flow logs tab and check whether any log exists or not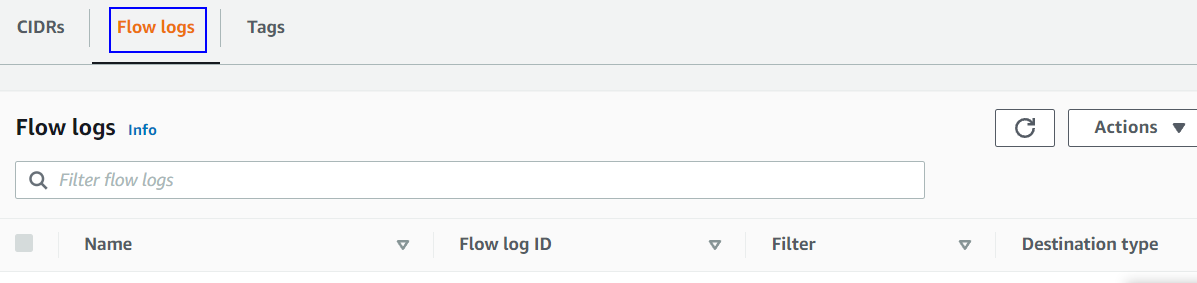
If you notice logging is not enabled do follow the remediation steps
Using AWS CLI:
aws ec2 describe-flow-logs
--filter "Name=<resource-id>,Values=<vpc-id>"Implementation Steps:
Sign in to the AWS management console
Navigate to VPC service at https://console.aws.amazon.com/vpc/
In the left navigation pane, select Your VPCs, You will see a list of VPCs that are already exists

Now select your desired VPC for which you want to enable VPC Flow Logs
Select the Flow logs tab and click on create flow log

6. Fill in all the details required as per your security norms to create the flow log as shown in the image
7. choose Destination Log group, IAM Role, Log Record format according to your requirement. And then click on create flow log
Note:-The Flow Logs are saved into log groups in CloudWatch Logs or to the S3 bucket as per the option you selected while creating the flow log.
Using AWS CLI:
To create flow logs
aws ec2 create-flow-logs
--resource-type VPC
--resource-ids <vpc-id>
--traffic-type ALL
--log-group-name <LogGroup>
--deliver-logs-permission-arn <arn>:role/<IAM Role>
Backout Plan:
Sign in to the management console
Navigate to VPC service at https://console.aws.amazon.com/vpc/
In the left navigation pane, select Your VPCs, You will see a list Of VPCs that are already exists
Select the log and click on the Actions button on the bottom right side, from the drop-down menu select Delete flow logs.

Using AWS CLI:
To delete flow logs
aws ec2 delete-flow-logs --flow-log-id fl-11223344556677889
Reference:
http://docs.aws.amazon.com/AmazonVPC/latest/UserGuide/flow-logs.html
CIS Controls:
6.2 Activate audit logging
Ensure that local logging has been enabled on all systems and networking devices.
12.5 Configure Monitoring Systems to Record Network Packets
Configure monitoring systems to record network packets passing through the boundary at each of the organization's network boundaries.
