Profile Applicability: Level 2
Description:
VPC Flow Logs is a feature that enables you to capture information about the IP traffic going to and from network interfaces in your VPC. After you've created a flow log, you can view and retrieve its data in Amazon CloudWatch Logs. It is recommended that VPC Flow Logs be enabled for packet "Rejects" for VPCs.
Rationale:
VPC Flow Logs provide visibility into network traffic that traverses the VPC and can be used to detect anomalous traffic or insight during security workflows.
Impact:
Once enabled, the Flow Logs feature will start collecting network traffic data to and from your Virtual Private Cloud (VPC), data that can be useful to detect and troubleshoot security issues and make sure that the network access rules are not overly permissive.
Default Value:
VPC flow is not enabled by default, Enabling VPC flow logs for all VPC Will increase the security and reduce compliance issues.
Audit:
Perform the following to determine if VPC Flow logs is enabled: Via the Management Console:
1. Sign into the AWS management console.
2. Navigate to VPC service at https://console.aws.amazon.com/vpc/
3. In the left navigation pane, select Your VPCs, You will see a list Of VPCs that already exists

4. Click on the VPC that you want to examine and select the Flow log tab and check whether any log exists or not.
5. If you notice logging is not enabled do follow the remediation steps.
Remediation:
Pre-Requisite:
There must be at least one VPC enabled in the AWS account.
Create Log Group in CloudWatch .
To enable Flow Logs for your VPC, you need to create first an IAM role that will grant permissions to publish flow log streams to the specified log group in CloudWatch Logs.
Ensure CloudWatch or S3 bucket is created for VPC flow log for retrieving the VPC flow log Data.
After auditing, if you notice logging is not enabled then only go to remediation steps.
Implementation Steps:
Perform the following to determine if VPC Flow logs is enabled: Via the Management Console:
1. Sign into the AWS management console
2. Navigate to VPC service at https://console.aws.amazon.com/vpc/
3.In the left navigation pane, select Your VPCs, You will see a list Of VPCs that are already exists
4.Now select your desired VPC for which you want to enable VPC Flow Logs
5. In the right pane, select the Flow Logs tab.
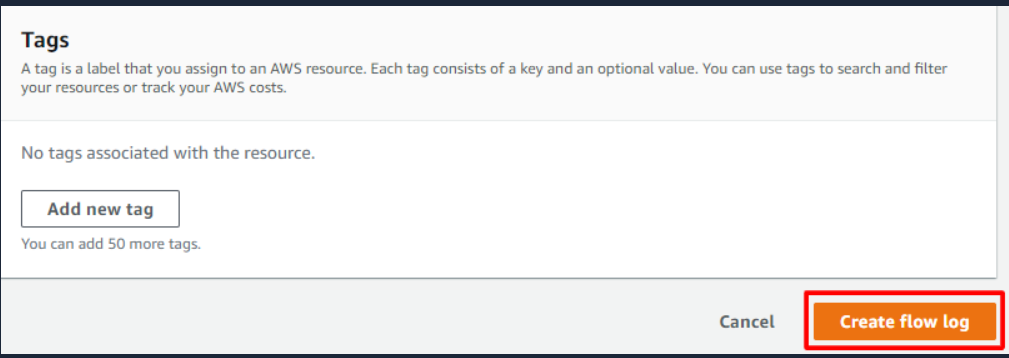
6. If no Flow Log exists, click Create Flow Log

7. For Filter, select Reject
8. Should have a Destination Log group or you have to create by going to CloudWatch in create log group and assign that log group in the flow log
9. Next you require IAM role with required policy for that it will grant permissions to publish flow log streams to the specified log group in CloudWatch Logs
10. And then click on create flow log
Note: Setting the filter to "Reject" will dramatically reduce the logging data accumulation for this recommendation and provide sufficient information for the purposes of breach detection, research and remediation. However, during periods of least privilege security group engineering, setting this the filter to "All" can be very helpful in discovering existing traffic flows required for proper operation of an already running environment.
Impact:
By default, CloudWatch Logs will store Logs indefinitely unless a specific retention period is defined for the log group. When choosing the number of days to retain, keep in mind the average days it takes an organization to realize they have been breached is 210 days (at the time of this writing). Since additional time is required to research a breach, a minimum 365 day retention policy allows time for detection and research. You may also wish to archive the logs to a cheaper storage service rather than simply deleting them. See the following AWS resource to manage CloudWatch Logs retention periods:
1. http://docs.aws.amazon.com/AmazonCloudWatch/latest/DeveloperGuide/SettingL ogRetention.html
Reference:
1. CCE-79202-8
2. CIS CSC v6.0 #6.5, #12.9
3. http://docs.aws.amazon.com/AmazonVPC/latest/UserGuide/flow-logs.html
Notes: Changed title from "Ensure VPC flow logging is enabled in all applicable regions" to "Ensure VPC flow logging is enabled in all VPCs" For these reasons:
1. Flow logs cannot be enabled for regions, only for VPCs
2. The statement did not define an "Applicable Region" and did not clarify "all VPCs in applicable regions"
3. All other benchmark recommendations appear to assume that you apply them "any actively used configuration or resource" or "All resources" - so specifying "applicable" to mean "active" or "compliant with the benchmark" seems unnecessary
CIS Controls:
6.2 Activate audit logging
Ensure that local logging has been enabled on all systems and networking devices.
12.5 Configure Monitoring Systems to Record Network Packets
Configure monitoring systems to record network packets passing through the boundary at each of the organization's network boundaries.
