Description:
This control ensures that Azure Storage Accounts are accessed through Private Endpoints, which provide private IP addresses within a virtual network (VNet). Private Endpoints enable secure, private connectivity between Azure Storage and trusted networks, reducing exposure to the public internet.
Rationale:
Enhances security by limiting storage access to private networks
Reduces risk of unauthorized access or data interception
Supports compliance requirements for network isolation of sensitive data
Impact:
Reduces the attack surface of Azure Storage Accounts
Improves overall security posture and data confidentiality
Default Value:
By default, Azure Storage Accounts allow public network access and do not require Private Endpoints.
Pre-requirements:
An existing Azure Storage Account
Permissions: Owner, Contributor, or Storage Account Contributor
Network permissions to create resources in the target VNet
Test Plan:
Sign in to the Microsoft Azure Portal:https://portal.azure.com
Navigate to Storage Accounts
Select the target storage account
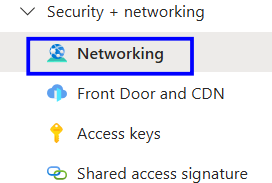
Under Security + networking, select Networking
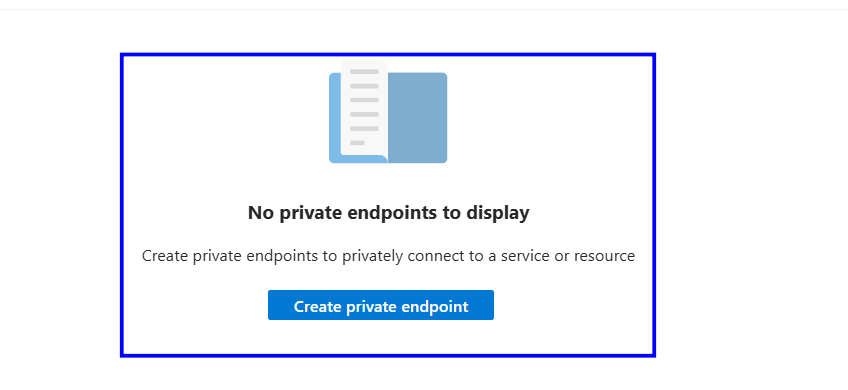
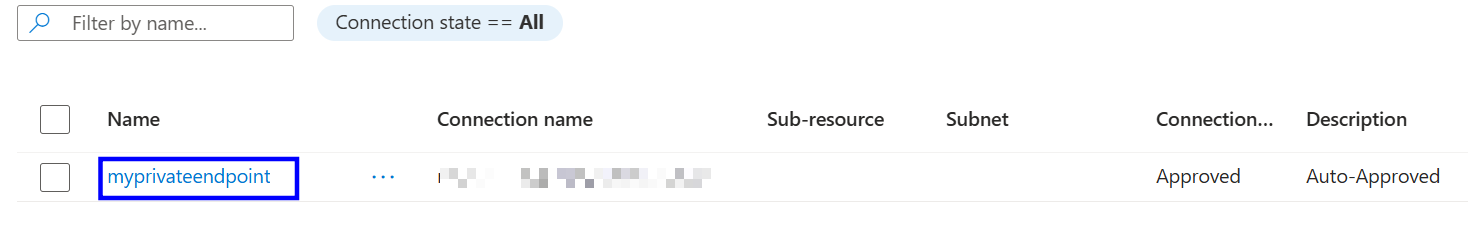
Verify that at least one Private Endpoint is configured for the storage account
If no Private Endpoint is configured, follow the implementation steps.
Implementation Steps:
Sign in to the Microsoft Azure Portal:https://portal.azure.com
Navigate to Storage Accounts
Select the target storage account
Under Security + networking, select Networking
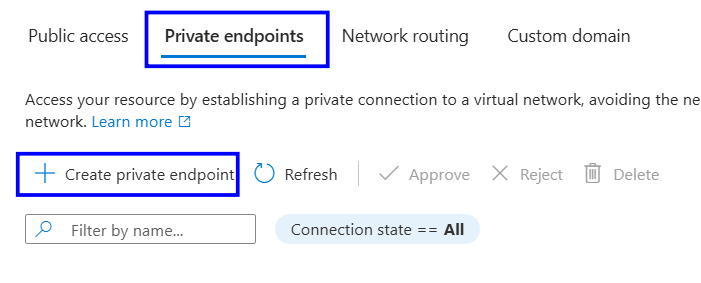
Select Private endpoint
Click + Private endpoint
Select the appropriate Resource Group, Virtual Network, and Subnet
Select the required storage service (for example, Blob)
Review the configuration and click Create
Backout Plan:
Sign in to the Microsoft Azure Portal
Navigate to Storage Accounts
Select the target storage account
Under Security + networking, select Networking
Select Private endpoint connections
Identify the configured Private Endpoint
Delete the Private Endpoint
Confirm changes are saved
Reference: